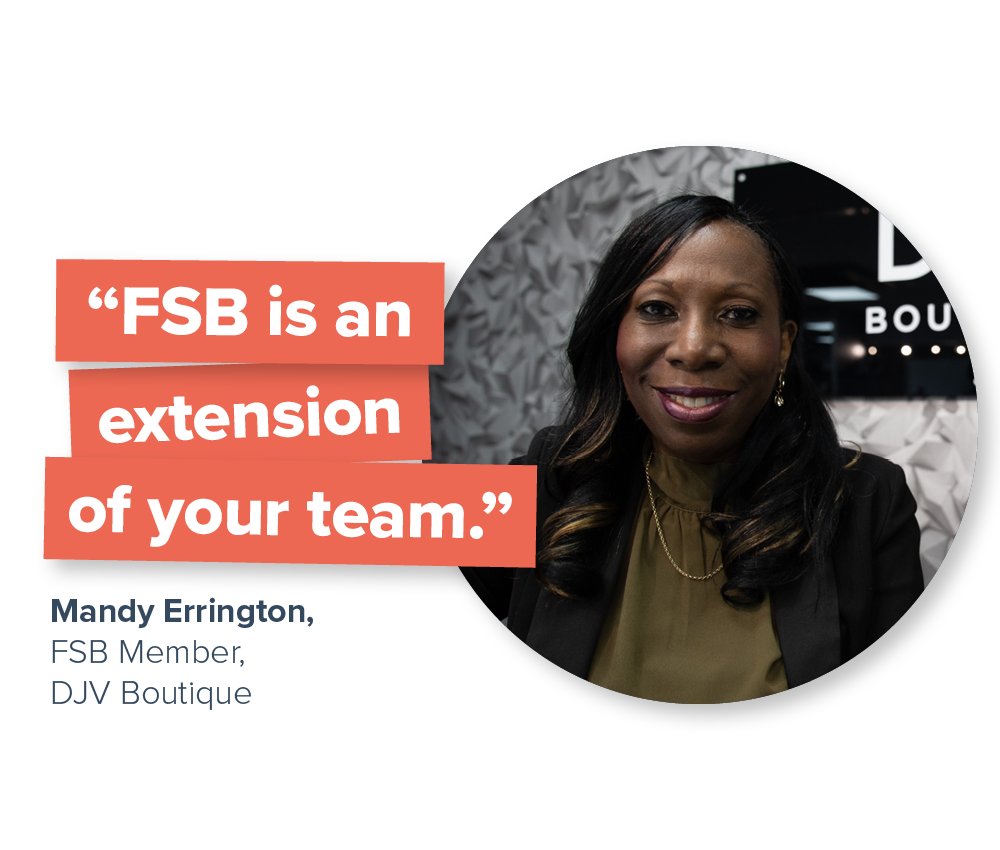
Trust the best with your business
Latest from the Federation of Small Businesses
Find the latest news
Stay in the loop with what's happening in the small business community across the UK, and discover our latest press releases on the issues that matter.
Attend an upcoming event
Join one of our popular national events or local networking meetings taking place across the UK every week. Learn new skills and connect with small business owners.
Learn new skills
Search our library of free resources, videos and downloadable guides. From legal compliance to digital marketing, grow your business with information from industry experts.